
Updates to your WordPress site become available all the time, whether for core files, themes, or plugins. Since many updates build on each other, the longer you wait to apply them, the greater the risk of compatibility issues or unexpected breakage.


Chatbots have become a standard part of how businesses interact with customers. From answering basic questions to supporting transactions and service requests, they’re now embedded across websites, apps, and internal systems.

Updates to your WordPress site become available all the time, whether for core files, themes, or plugins. Since many updates build on each other, the longer you wait to apply them, the greater the risk of compatibility issues or unexpected breakage.


From collecting information to completing orders, web forms provide a wealth of opportunities to connect with and learn about consumers. Unfortunately, these forms can be as risky as they are helpful. Not only are they incredibly vulnerable to attacks, but they are also frequently overlooked when developing website security solutions.

Reliant on social engineering, SocGholish has become a widely used malware framework in cybercrime. This type of cyberattack can take advantage of trustworthy sites and seemingly legitimate emails to infect users’ devices with malware.
WordPress delivers extensive personalization, scalability, and community support, but with a caveat: WordPress sites can be incredibly vulnerable. The very flexibility that makes this content management system (CMS) so appealing can deliver added risks: vulnerability exploits, brute force attacks, and SQL injection attacks, to name a few.
400 Bad Request errors are a common HTTP error that WordPress website owners encounter. If you want to prevent downtime and keep your WordPress site running smoothly, knowing how to fix these and other common WordPress errors is key. While the error is returned by the server, it is most often triggered by a problem with the request itself, making it a client error related to malformed syntax, invalid data, or other client-side issues. If left unresolved, these errors can lead to user frustration and a poor user experience.
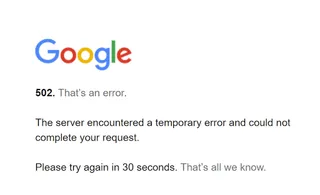
Website reliability is a paramount priority for business owners, and avoiding common errors that can disrupt website functionality is a key place to start. 500 errors, in particular, can often render a website inoperable, resulting in consequences such as poor user experience, damage to search engine optimization (SEO) rankings, and a lot more.

Chances are, you’ve heard about the dangers of an insecure website. You could also be asking yourself, “Why does my website say not secure?” or wondering what it means when a website is not secure. Discover what cybersecurity experts really mean when they say a site is “not secure” and how to improve your site’s overall security.

A distributed denial-of-service attack, also known as a DDoS attack, is a malicious attempt that occurs when a large volume of automated requests overwhelms a server or network and prevents normal access to your website for real visitors. In a matter of minutes, this flood of traffic can disrupt performance and bring your website to a grinding halt.

Website security measures provide critical peace of mind as you protect your web presence against hackers, data breaches, and other cyberattacks. Without strict security protocols, you risk viruses, malware infections, and a whole host of other problems that leave your website, your customers, and your reputation at risk.
