Pluginsmonsters Fake Plugin Allows Access to WordPress Sites


The SiteLock Research team has become aware of sites infected with fake WordPress plugins that provide cybercriminals with backdoor access and allow them to inject malicious content onto web pages. Below is a high-level overview of the plugins and malware being detected by our scanners and analyzed by SiteLock Research analysts. We also cover effective tips to help protect your site.

What It’s Doing
The fake plugins have names that include ‘pluginmonsters’, ‘pluginsamonsters’ (note the ‘a’), and ‘ls-oembed’ and are followed by similarly named files that contain malicious injectors.
- /wp-content/plugins/all-in-one-wp-security-and-firewall/all-in-one-wp-security-and-firewall.php
- /wp-content/plugins/ls-oembed/ls-oembed.php
- /wp-content/plugins/pluginmonsters/pluginmonsters.php
- /wp-content/plugins/pluginsmonsters/pluginsmonsters.php
- /wp-content/plugins/pluginsamonsters/pluginsamonsters.php
Likely through a vulnerable plugin, the fraudulent plugins are written to the wp-content/plugins directory. Each plugin includes a similarly named file containing the primary malware payload, a zero-byte file named file.txt, proxy.txt, or security.txt, and a data directory which contains a malicious uploader named index.php.
The main plugin file, here pluginsmonsters.php, starts with header comments that reference Scratch, MIT’s learning-focused programming language. The active code then defines the plugin’s location and other variables, and sets up a function, SECURITYFIREWALL_hide. The function returns the complete list of plugins depending on the attacker’s $_GET parameter of SECURITYFIREWALL__ADMIN_LOGIN. More importantly, it checks if the plugin is active, and if so, hides itself with unset().
The pluginsmonsters file then hooks the SECURITYFIREWALL_hide function into the all_plugins filter, hiding itself in WordPress’ plugins table within the MySQL database. The final capability is to hook an anonymous function to loop_start to output the file.txt file contents as WordPress shows posts.

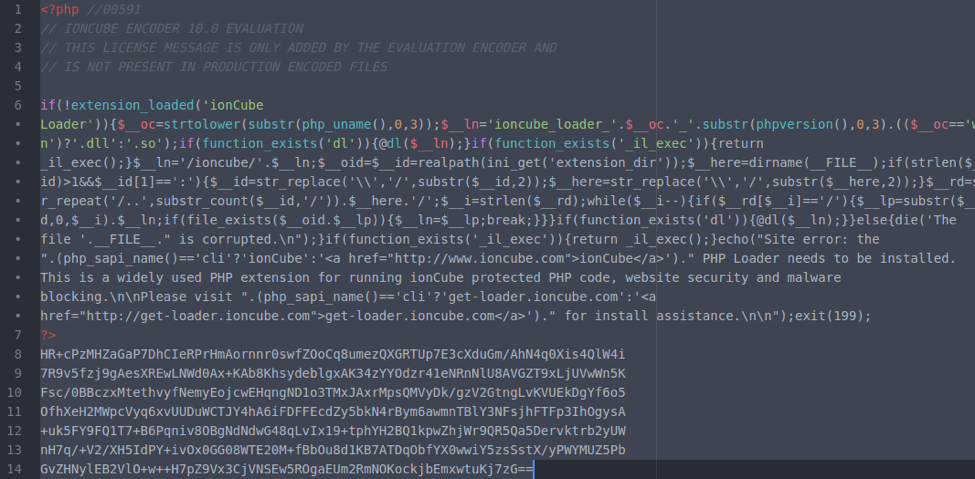
Content of the file pluginsmonsters.php
The data/index.php file is an uploader with two methods to upload files to the infected site, using move_uploaded_file() if the $_POST upload parameter is set to ‘1’, and fwrite() if upload is set to ‘2’.
Content of /data/index.php with the fake plugin’s folder
Additional files which may be associated with the plugin infections, include the same uploader files and fped8.org doorway scripts in the /wp-content directory. These additional files can be used to upload or inject malicious content into the site.
- php
- wp-acsesapps.php
- php
- php
- wp-trackbacksys.php
- php
It is important to note that attack kits, such as these fake plugins, often change their plugin names and file names to avoid detection. This makes using a file-based malware scanner that detects file content, rather than file names, an important part of any security response to this type of threat.
Protecting Your Site
Protecting against ‘pluginsmonsters’ and similar infections starts with keeping core WordPress, plugins, and themes up-to-date. In Q4 2017, only 46% of WordPress sites infected with malware were found to be running the latest core updates. It is also a best practice to familiarize yourself with your website files using a hosting provider’s file manager or FTP. This allows you to periodically review the files in your site’s /wp-content/plugins directory for suspicious content you did not install.
Finally, implement a proactive security plan that includes a Web Application Firewall (WAF) and daily malware scanner. Using a WAF to protect your site will filter bot and malicious traffic before attackers have a chance to access your site. Malware scanners, such as SiteLock SMARTPLUS, will scan your website files daily and automatically remove any malicious content upon detection. SMART® PLUS™ also proactively protects your website by patching core Content Management System (CMS) vulnerabilities and scanning WordPress databases for malicious and spam content.
For more information on protecting your WordPress sites from fake plugins and other threats, call SiteLock at 855.378.6200 and ask about SMART® PLUS™. We’re available 24/7/365 to answer your calls or live chats.